AWX is a one of the great devops and orchestration tool for deployment and configuration management. With Ansible AWX Tower you can unify and regulate your LAB Dev IT organization with a graphic dashboard, RBAC (role-based access control) , job scheduling, integrated announcements and graphical inventory administration and management. Effortlessly insert Ansible AWX Tower into current tools and procedures with REST API and CLI. AWX provides a web-based user interface, REST API, and task engine built on top of Ansible. It is one of the upstream projects for Red Hat Ansible Automation Platform.
Install Ansible AWX on Microsoft Windows OS
The AWX Project - AWX for short -- is an open source community project, backed by Red Hat, that permits users to better control their Ansible project use in IT environments. AWX is the upstream project from which the Red Hat Ansible Tower offering is ultimately derived.
Before preparing and installing AWX on Ubuntu OS make sure you have minimum hardware on your system as below, I am installing AWX on VMware ESXi virtual machine.
4 CPU
12 GB RAM
30 GB Disk Drive space
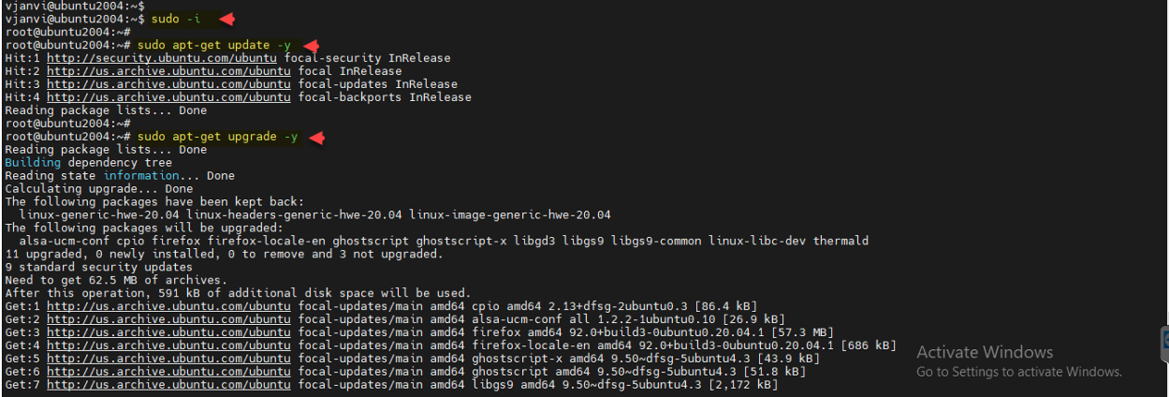
Before staring installation I switched to sudo and upgraded and updated Ubuntu operating system using apt-get.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 |
vjanvi@ubuntu2004:~$ sudo -i root@ubuntu2004:~# root@ubuntu2004:~# sudo apt-get update -y Hit:1 http://security.ubuntu.com/ubuntu focal-security InRelease Hit:2 http://us.archive.ubuntu.com/ubuntu focal InRelease Hit:3 http://us.archive.ubuntu.com/ubuntu focal-updates InRelease Hit:4 http://us.archive.ubuntu.com/ubuntu focal-backports InRelease Reading package lists... Done root@ubuntu2004:~# root@ubuntu2004:~# sudo apt-get upgrade -y Reading package lists... Done Building dependency tree Reading state information... Done Calculating upgrade... Done The following packages have been kept back: linux-generic-hwe-20.04 linux-headers-generic-hwe-20.04 linux-image-generic-hwe-20.04 The following packages will be upgraded: alsa-ucm-conf cpio firefox firefox-locale-en ghostscript ghostscript-x libgd3 libgs9 libgs9-common linux-libc-dev thermald 11 upgraded, 0 newly installed, 0 to remove and 3 not upgraded. 9 standard security updates Need to get 62.5 MB of archives. After this operation, 591 kB of additional disk space will be used. Get:1 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 cpio amd64 2.13+dfsg-2ubuntu0.3 [86.4 kB] Get:2 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 alsa-ucm-conf all 1.2.2-1ubuntu0.10 [26.9 kB] Get:3 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 firefox amd64 92.0+build3-0ubuntu0.20.04.1 [57.3 MB] Get:4 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 firefox-locale-en amd64 92.0+build3-0ubuntu0.20.04.1 [686 kB] Get:5 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 ghostscript-x amd64 9.50~dfsg-5ubuntu4.3 [43.9 kB] Get:6 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 ghostscript amd64 9.50~dfsg-5ubuntu4.3 [51.8 kB] Get:7 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 libgs9 amd64 9.50~dfsg-5ubuntu4.3 [2,172 kB] Get:8 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 libgs9-common all 9.50~dfsg-5ubuntu4.3 [681 kB] Get:9 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 libgd3 amd64 2.2.5-5.2ubuntu2.1 [118 kB] Get:10 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 linux-libc-dev amd64 5.4.0-84.94 [1,115 kB] Get:11 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 thermald amd64 1.9.1-1ubuntu0.6 [233 kB] Fetched 62.5 MB in 1s (48.9 MB/s) (Reading database ... 192284 files and directories currently installed.) Preparing to unpack .../00-cpio_2.13+dfsg-2ubuntu0.3_amd64.deb ... Unpacking cpio (2.13+dfsg-2ubuntu0.3) over (2.13+dfsg-2) ... Preparing to unpack .../01-alsa-ucm-conf_1.2.2-1ubuntu0.10_all.deb ... Unpacking alsa-ucm-conf (1.2.2-1ubuntu0.10) over (1.2.2-1ubuntu0.9) ... Preparing to unpack .../02-firefox_92.0+build3-0ubuntu0.20.04.1_amd64.deb ... Unpacking firefox (92.0+build3-0ubuntu0.20.04.1) over (91.0.2+build1-0ubuntu0.20.04.1) ... Preparing to unpack .../03-firefox-locale-en_92.0+build3-0ubuntu0.20.04.1_amd64.deb ... Unpacking firefox-locale-en (92.0+build3-0ubuntu0.20.04.1) over (91.0.2+build1-0ubuntu0.20.04.1) ... Preparing to unpack .../04-ghostscript-x_9.50~dfsg-5ubuntu4.3_amd64.deb ... Unpacking ghostscript-x (9.50~dfsg-5ubuntu4.3) over (9.50~dfsg-5ubuntu4.2) ... Preparing to unpack .../05-ghostscript_9.50~dfsg-5ubuntu4.3_amd64.deb ... Unpacking ghostscript (9.50~dfsg-5ubuntu4.3) over (9.50~dfsg-5ubuntu4.2) ... Preparing to unpack .../06-libgs9_9.50~dfsg-5ubuntu4.3_amd64.deb ... Unpacking libgs9:amd64 (9.50~dfsg-5ubuntu4.3) over (9.50~dfsg-5ubuntu4.2) ... Preparing to unpack .../07-libgs9-common_9.50~dfsg-5ubuntu4.3_all.deb ... Unpacking libgs9-common (9.50~dfsg-5ubuntu4.3) over (9.50~dfsg-5ubuntu4.2) ... Preparing to unpack .../08-libgd3_2.2.5-5.2ubuntu2.1_amd64.deb ... Unpacking libgd3:amd64 (2.2.5-5.2ubuntu2.1) over (2.2.5-5.2ubuntu2) ... Preparing to unpack .../09-linux-libc-dev_5.4.0-84.94_amd64.deb ... Unpacking linux-libc-dev:amd64 (5.4.0-84.94) over (5.4.0-81.91) ... Preparing to unpack .../10-thermald_1.9.1-1ubuntu0.6_amd64.deb ... Unpacking thermald (1.9.1-1ubuntu0.6) over (1.9.1-1ubuntu0.5) ... Setting up libgs9-common (9.50~dfsg-5ubuntu4.3) ... Setting up cpio (2.13+dfsg-2ubuntu0.3) ... Setting up libgs9:amd64 (9.50~dfsg-5ubuntu4.3) ... Setting up firefox (92.0+build3-0ubuntu0.20.04.1) ... Please restart all running instances of firefox, or you will experience problems. Setting up alsa-ucm-conf (1.2.2-1ubuntu0.10) ... Setting up linux-libc-dev:amd64 (5.4.0-84.94) ... Setting up ghostscript (9.50~dfsg-5ubuntu4.3) ... Setting up firefox-locale-en (92.0+build3-0ubuntu0.20.04.1) ... Setting up libgd3:amd64 (2.2.5-5.2ubuntu2.1) ... Setting up thermald (1.9.1-1ubuntu0.6) ... Setting up ghostscript-x (9.50~dfsg-5ubuntu4.3) ... Processing triggers for dbus (1.12.16-2ubuntu2.1) ... Processing triggers for desktop-file-utils (0.24-1ubuntu3) ... Processing triggers for mime-support (3.64ubuntu1) ... Processing triggers for hicolor-icon-theme (0.17-2) ... Processing triggers for gnome-menus (3.36.0-1ubuntu1) ... Processing triggers for libc-bin (2.31-0ubuntu9.2) ... Processing triggers for man-db (2.9.1-1) ... root@ubuntu2004:~# |
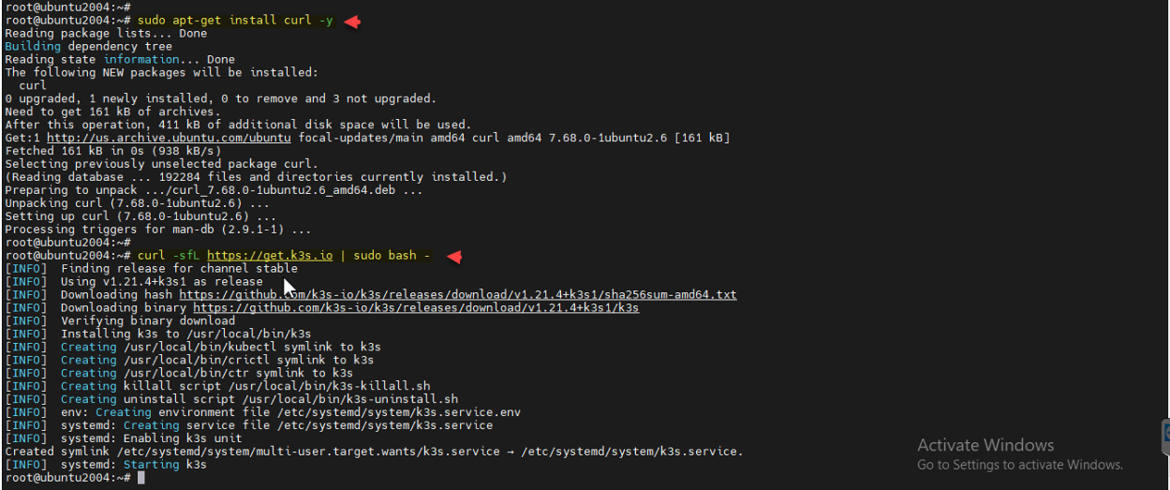
I am going to install Ansible AWX server as a containers on k3s (It is lightweight trimmed down k8s [Kubernetes] version), to download k3s I need curl tool which I have installed with apt-get command. Downloaded and installed k3s from https://get.k3s.io url.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 |
root@ubuntu2004:~# root@ubuntu2004:~# sudo apt-get install curl -y Reading package lists... Done Building dependency tree Reading state information... Done The following NEW packages will be installed: curl 0 upgraded, 1 newly installed, 0 to remove and 3 not upgraded. Need to get 161 kB of archives. After this operation, 411 kB of additional disk space will be used. Get:1 http://us.archive.ubuntu.com/ubuntu focal-updates/main amd64 curl amd64 7.68.0-1ubuntu2.6 [161 kB] Fetched 161 kB in 0s (938 kB/s) Selecting previously unselected package curl. (Reading database ... 192284 files and directories currently installed.) Preparing to unpack .../curl_7.68.0-1ubuntu2.6_amd64.deb ... Unpacking curl (7.68.0-1ubuntu2.6) ... Setting up curl (7.68.0-1ubuntu2.6) ... Processing triggers for man-db (2.9.1-1) ... root@ubuntu2004:~# root@ubuntu2004:~# curl -sfL https://get.k3s.io | sudo bash - [INFO] Finding release for channel stable [INFO] Using v1.21.4+k3s1 as release [INFO] Downloading hash https://github.com/k3s-io/k3s/releases/download/v1.21.4+k3s1/sha256sum-amd64.txt [INFO] Downloading binary https://github.com/k3s-io/k3s/releases/download/v1.21.4+k3s1/k3s [INFO] Verifying binary download [INFO] Installing k3s to /usr/local/bin/k3s [INFO] Creating /usr/local/bin/kubectl symlink to k3s [INFO] Creating /usr/local/bin/crictl symlink to k3s [INFO] Creating /usr/local/bin/ctr symlink to k3s [INFO] Creating killall script /usr/local/bin/k3s-killall.sh [INFO] Creating uninstall script /usr/local/bin/k3s-uninstall.sh [INFO] env: Creating environment file /etc/systemd/system/k3s.service.env [INFO] systemd: Creating service file /etc/systemd/system/k3s.service [INFO] systemd: Enabling k3s unit Created symlink /etc/systemd/system/multi-user.target.wants/k3s.service → /etc/systemd/system/k3s.service. [INFO] systemd: Starting k3s root@ubuntu2004:~# root@ubuntu2004:~# |
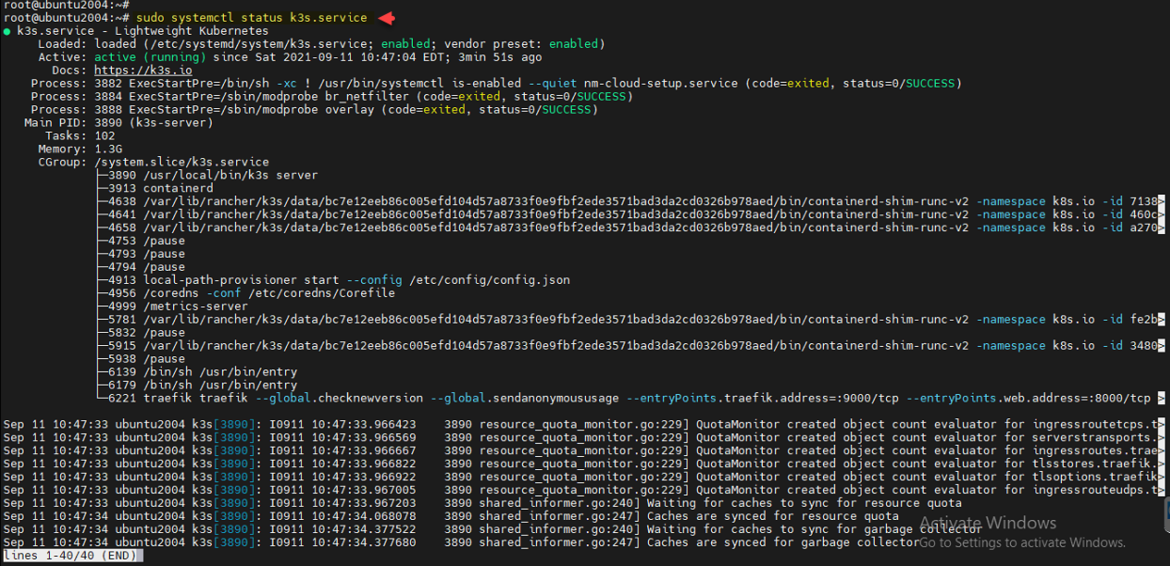
Once k3s is installed make sure service is started, status can be checked with systemctl command. press q to quit logs.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 |
root@ubuntu2004:~# sudo systemctl status k3s.service ● k3s.service - Lightweight Kubernetes Loaded: loaded (/etc/systemd/system/k3s.service; enabled; vendor preset: enabled) Active: active (running) since Sat 2021-09-11 10:47:04 EDT; 3min 51s ago Docs: https://k3s.io Process: 3882 ExecStartPre=/bin/sh -xc ! /usr/bin/systemctl is-enabled --quiet nm-cloud-setup.service (code=exited, status=0/SUCCESS) Process: 3884 ExecStartPre=/sbin/modprobe br_netfilter (code=exited, status=0/SUCCESS) Process: 3888 ExecStartPre=/sbin/modprobe overlay (code=exited, status=0/SUCCESS) Main PID: 3890 (k3s-server) Tasks: 102 Memory: 1.3G CGroup: /system.slice/k3s.service ├─3890 /usr/local/bin/k3s server ├─3913 containerd ├─4638 /var/lib/rancher/k3s/data/bc7e12eeb86c005efd104d57a8733f0e9fbf2ede3571bad3da2cd0326b978aed/bin/containerd-shim-runc-v2 -namespace k8s.io -id 7138> ├─4641 /var/lib/rancher/k3s/data/bc7e12eeb86c005efd104d57a8733f0e9fbf2ede3571bad3da2cd0326b978aed/bin/containerd-shim-runc-v2 -namespace k8s.io -id 460c> ├─4658 /var/lib/rancher/k3s/data/bc7e12eeb86c005efd104d57a8733f0e9fbf2ede3571bad3da2cd0326b978aed/bin/containerd-shim-runc-v2 -namespace k8s.io -id a270> ├─4753 /pause ├─4793 /pause ├─4794 /pause ├─4913 local-path-provisioner start --config /etc/config/config.json ├─4956 /coredns -conf /etc/coredns/Corefile ├─4999 /metrics-server ├─5781 /var/lib/rancher/k3s/data/bc7e12eeb86c005efd104d57a8733f0e9fbf2ede3571bad3da2cd0326b978aed/bin/containerd-shim-runc-v2 -namespace k8s.io -id fe2b> ├─5832 /pause ├─5915 /var/lib/rancher/k3s/data/bc7e12eeb86c005efd104d57a8733f0e9fbf2ede3571bad3da2cd0326b978aed/bin/containerd-shim-runc-v2 -namespace k8s.io -id 3480> ├─5938 /pause ├─6139 /bin/sh /usr/bin/entry ├─6179 /bin/sh /usr/bin/entry └─6221 traefik traefik --global.checknewversion --global.sendanonymoususage --entryPoints.traefik.address=:9000/tcp --entryPoints.web.address=:8000/tcp > Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.966423 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for ingressroutetcps.t> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.966569 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for serverstransports.> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.966667 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for ingressroutes.trae> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.966822 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for tlsstores.traefik.> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.966922 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for tlsoptions.traefik> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.967005 3890 resource_quota_monitor.go:229] QuotaMonitor created object count evaluator for ingressrouteudps.t> Sep 11 10:47:33 ubuntu2004 k3s[3890]: I0911 10:47:33.967203 3890 shared_informer.go:240] Waiting for caches to sync for resource quota Sep 11 10:47:34 ubuntu2004 k3s[3890]: I0911 10:47:34.068078 3890 shared_informer.go:247] Caches are synced for resource quota Sep 11 10:47:34 ubuntu2004 k3s[3890]: I0911 10:47:34.377522 3890 shared_informer.go:240] Waiting for caches to sync for garbage collector Sep 11 10:47:34 ubuntu2004 k3s[3890]: I0911 10:47:34.377680 3890 shared_informer.go:247] Caches are synced for garbage collector root@ubuntu2004:~# |
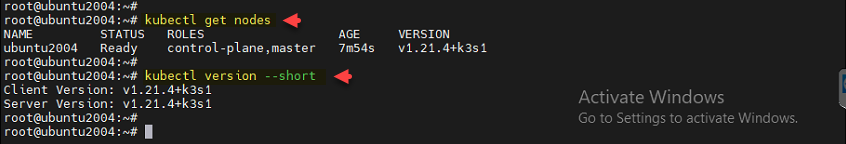
Verify k3s containers are working fine with getting nodes and version with kubectl commands.
1 2 3 4 5 6 7 8 9 |
root@ubuntu2004:~# root@ubuntu2004:~# kubectl get nodes NAME STATUS ROLES AGE VERSION ubuntu2004 Ready control-plane,master 7m54s v1.21.4+k3s1 root@ubuntu2004:~# root@ubuntu2004:~# kubectl version --short Client Version: v1.21.4+k3s1 Server Version: v1.21.4+k3s1 root@ubuntu2004:~# |
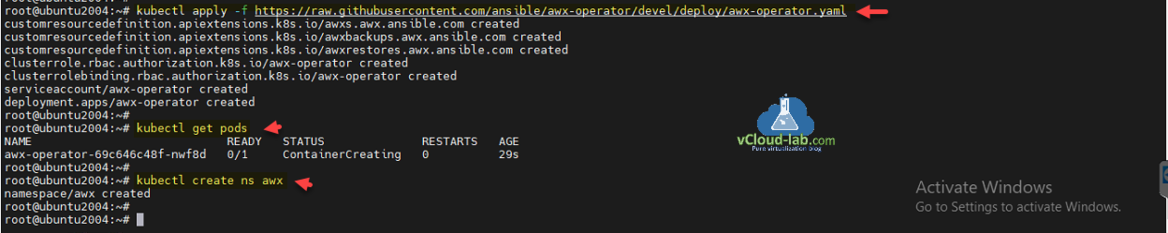
Ansible AWX is called awx-operator. Apply the configuration awx-operator.yaml from github url with kubectl by creating pods on the k3s cluster. verify containers/pods are created. Create a new namespace called awx.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
root@ubuntu2004:~# root@ubuntu2004:~# kubectl apply -f https://raw.githubusercontent.com/ansible/awx-operator/devel/deploy/awx-operator.yaml customresourcedefinition.apiextensions.k8s.io/awxs.awx.ansible.com created customresourcedefinition.apiextensions.k8s.io/awxbackups.awx.ansible.com created customresourcedefinition.apiextensions.k8s.io/awxrestores.awx.ansible.com created clusterrole.rbac.authorization.k8s.io/awx-operator created clusterrolebinding.rbac.authorization.k8s.io/awx-operator created serviceaccount/awx-operator created deployment.apps/awx-operator created root@ubuntu2004:~# root@ubuntu2004:~# kubectl get pods NAME READY STATUS RESTARTS AGE awx-operator-69c646c48f-nwf8d 0/1 ContainerCreating 0 29s root@ubuntu2004:~# root@ubuntu2004:~# kubectl create ns awx namespace/awx created root@ubuntu2004:~# |
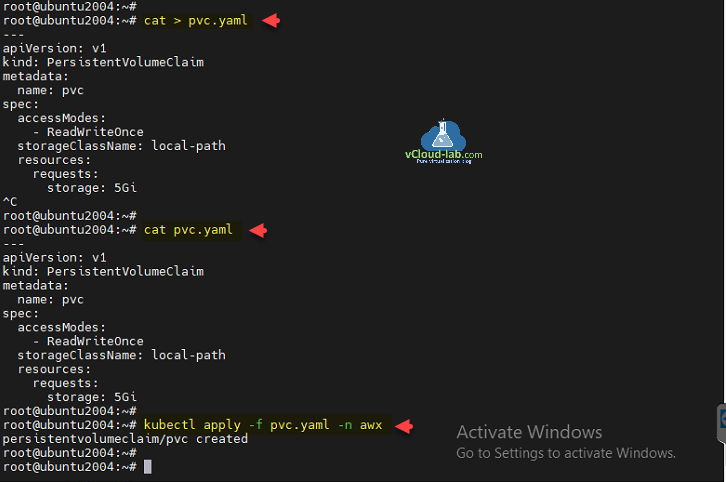
Create a pvc.yaml file with below yaml configuration to create a PersistentVolumeClaim. Apply them with kubectl command on k3s cluster.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 |
root@ubuntu2004:~# cat > pvc.yaml --- apiVersion: v1 kind: PersistentVolumeClaim metadata: name: pvc spec: accessModes: - ReadWriteOnce storageClassName: local-path resources: requests: storage: 5Gi ^C root@ubuntu2004:~# root@ubuntu2004:~# cat pvc.yaml --- apiVersion: v1 kind: PersistentVolumeClaim metadata: name: pvc spec: accessModes: - ReadWriteOnce storageClassName: local-path resources: requests: storage: 5Gi root@ubuntu2004:~# root@ubuntu2004:~# kubectl apply -f pvc.yaml -n awx persistentvolumeclaim/pvc created |
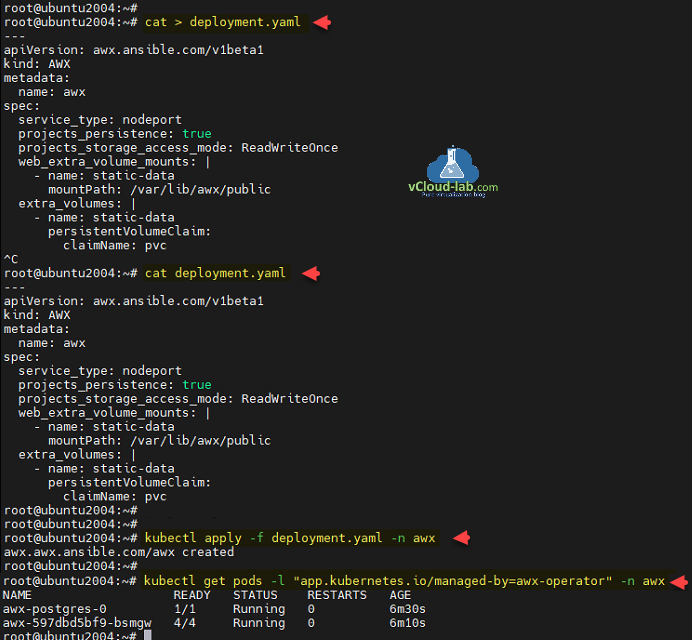
Create another file deployment.yaml and apply with kubectl to create additional nodeport service.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 |
root@ubuntu2004:~# kubectl get pvc -n awx NAME STATUS VOLUME CAPACITY ACCESS MODES STORAGECLASS AGE pvc Pending local-path 3m26s root@ubuntu2004:~# root@ubuntu2004:~# cat > deployment.yaml --- apiVersion: awx.ansible.com/v1beta1 kind: AWX metadata: name: awx spec: service_type: nodeport projects_persistence: true projects_storage_access_mode: ReadWriteOnce web_extra_volume_mounts: | - name: static-data mountPath: /var/lib/awx/public extra_volumes: | - name: static-data persistentVolumeClaim: claimName: pvc ^C root@ubuntu2004:~# cat deployment.yaml --- apiVersion: awx.ansible.com/v1beta1 kind: AWX metadata: name: awx spec: service_type: nodeport projects_persistence: true projects_storage_access_mode: ReadWriteOnce web_extra_volume_mounts: | - name: static-data mountPath: /var/lib/awx/public extra_volumes: | - name: static-data persistentVolumeClaim: claimName: pvc root@ubuntu2004:~# root@ubuntu2004:~# kubectl apply -f deployment.yaml -n awx awx.awx.ansible.com/awx created root@ubuntu2004:~# root@ubuntu2004:~# kubectl get pods -l "app.kubernetes.io/managed-by=awx-operator" -n awx NAME READY STATUS RESTARTS AGE awx-postgres-0 1/1 Running 0 6m30s awx-597dbd5bf9-bsmgw 4/4 Running 0 6m10s root@ubuntu2004:~# |
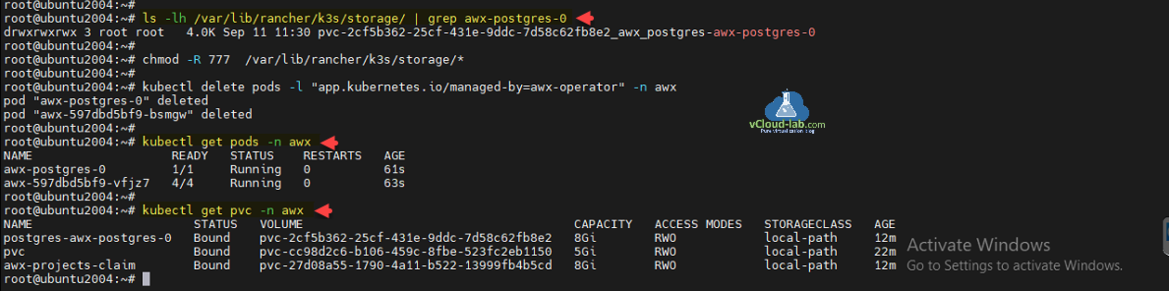
I am running below commands to fix error permission denied while accessing postgres database before doing further configuration.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
root@ubuntu2004:~# ls -lh /var/lib/rancher/k3s/storage/ | grep awx-postgres-0 drwxrwxrwx 3 root root 4.0K Sep 11 11:30 pvc-2cf5b362-25cf-431e-9ddc-7d58c62fb8e2_awx_postgres-awx-postgres-0 root@ubuntu2004:~# root@ubuntu2004:~# chmod -R 777 /var/lib/rancher/k3s/storage/* root@ubuntu2004:~# root@ubuntu2004:~# kubectl delete pods -l "app.kubernetes.io/managed-by=awx-operator" -n awx pod "awx-postgres-0" deleted pod "awx-597dbd5bf9-bsmgw" deleted root@ubuntu2004:~# root@ubuntu2004:~# kubectl get pods -n awx NAME READY STATUS RESTARTS AGE awx-postgres-0 1/1 Running 0 61s awx-597dbd5bf9-vfjz7 4/4 Running 0 63s root@ubuntu2004:~# root@ubuntu2004:~# kubectl get pvc -n awx NAME STATUS VOLUME CAPACITY ACCESS MODES STORAGECLASS AGE postgres-awx-postgres-0 Bound pvc-2cf5b362-25cf-431e-9ddc-7d58c62fb8e2 8Gi RWO local-path 12m pvc Bound pvc-cc98d2c6-b106-459c-8fbe-523fc2eb1150 5Gi RWO local-path 22m awx-projects-claim Bound pvc-27d08a55-1790-4a11-b522-13999fb4b5cd 8Gi RWO local-path 12m root@ubuntu2004:~# |
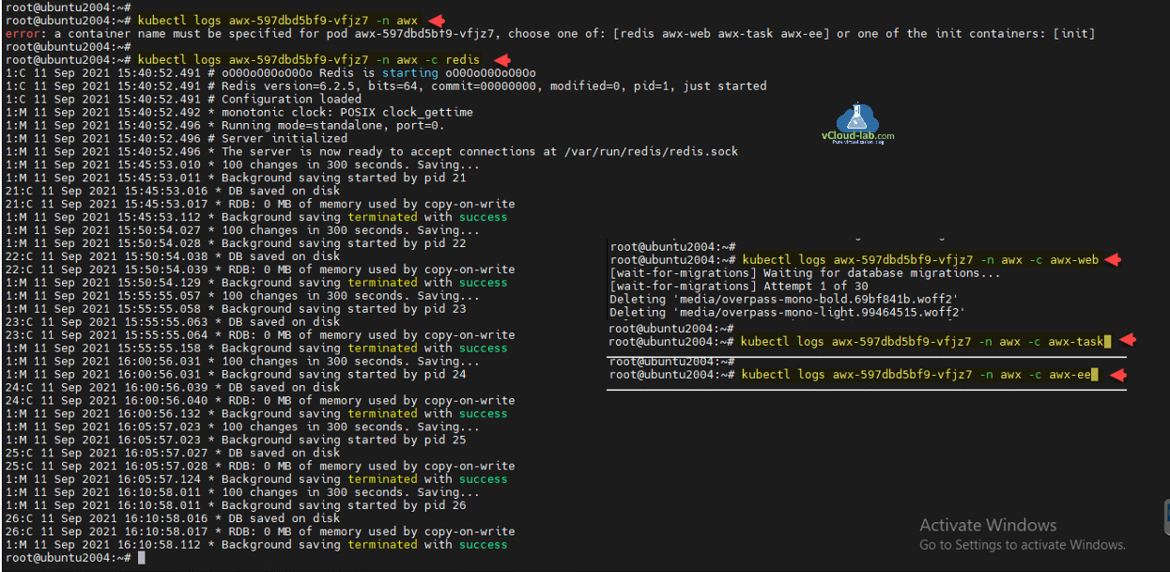
Provide containers a name with below commands.
kubectl logs awx-597dbd5bf9-vfjz7 -n awx kubectl logs awx-597dbd5bf9-vfjz7 -n awx -c redis kubectl logs awx-597dbd5bf9-vfjz7 -n awx -c awx-web kubectl logs awx-597dbd5bf9-vfjz7 -n awx -c awx-task kubectl logs awx-597dbd5bf9-vfjz7 -n awx -c awx-ee
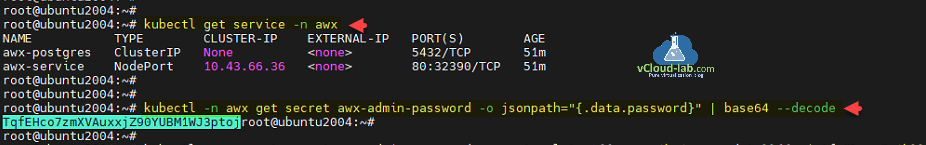
Check the service details with kubectl, you will find the port details mapping of awx-service. In my case I am using the port number 32390 with my Ubuntu server ip address to access Ansible AWX portal. You will need secret password to access awx portal, which you can get and decode with below command.
1 2 3 4 5 6 7 8 |
root@ubuntu2004:~# kubectl get service -n awx NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE awx-postgres ClusterIP None <none> 5432/TCP 51m awx-service NodePort 10.43.66.36 <none> 80:32390/TCP 51m root@ubuntu2004:~# root@ubuntu2004:~# root@ubuntu2004:~# kubectl -n awx get secret awx-admin-password -o jsonpath="{.data.password}" | base64 --decode TqfEHco7zmXVAuxxjZ90YUBM1WJ3ptojroot@ubuntu2004:~# |
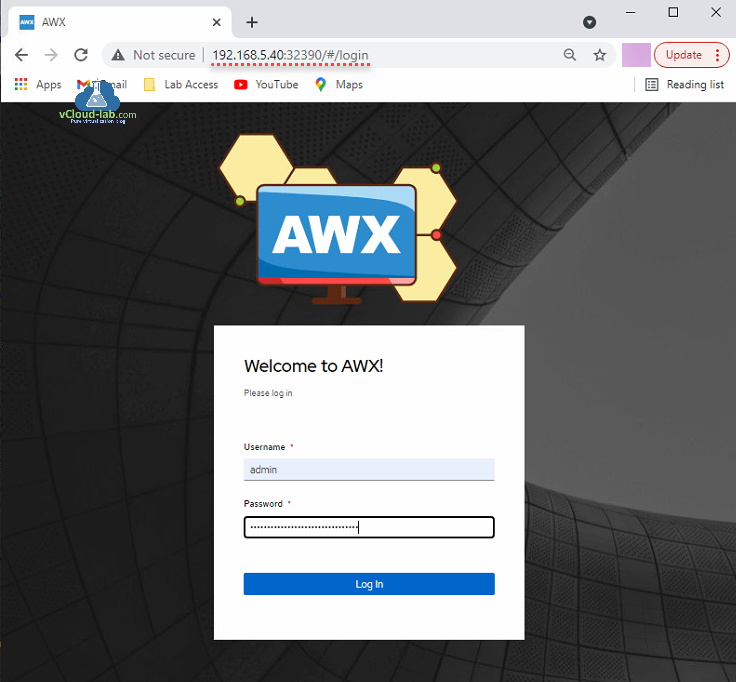
Use browser to access AWX portal and use username as admin and password decoded earlier to login.
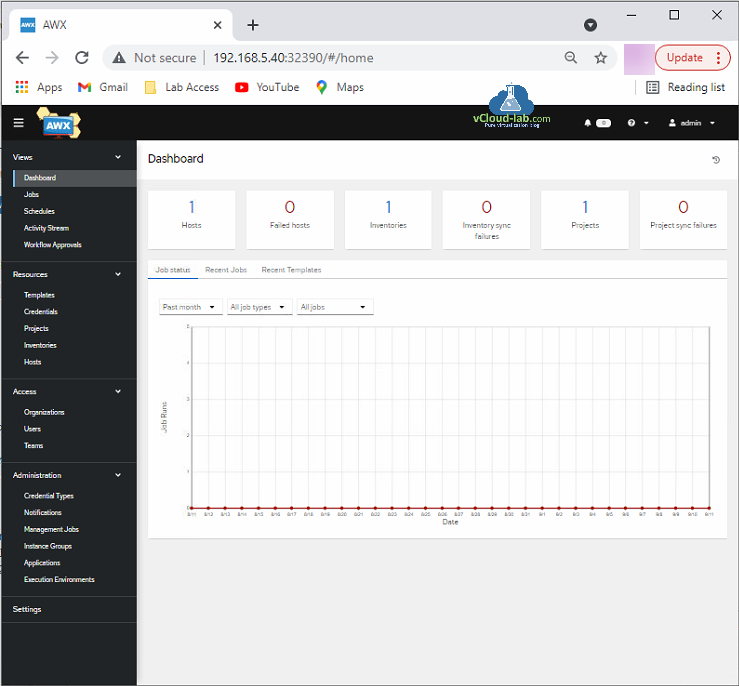
I am able to authenticate and login onto awx successfully.
Useful Articles
Getting started Ansible AWX tower for IT automation run first playbook
Ansible for VMwary Using vmware_vm_inventory dynamic inventory plugin
Ansible selectattr The error was TemplateRuntimeError no test named 'equalto'
ansible create an array with set_fact
Ansible get information from esxi advanced settings nested dictionary with unique keynames
Install Ansible AWX Tower on Ubuntu Linux
Ansible AWX installation error Cannot have both the docker-py and docker python modules
Ansible AWX installation error docker-compose run --rm --service-ports task awx-manage migrate --no-input
docker: Got permission denied while trying to connect to the Docker daemon socket
Ansible AWX Tower create Manual SCM (Source Control Credential Type) project
Reset Ansible AWX Tower admin password
Install Ansible AWX on Microsoft Windows OS
Step by Step Install Ansible on Ubuntu OS