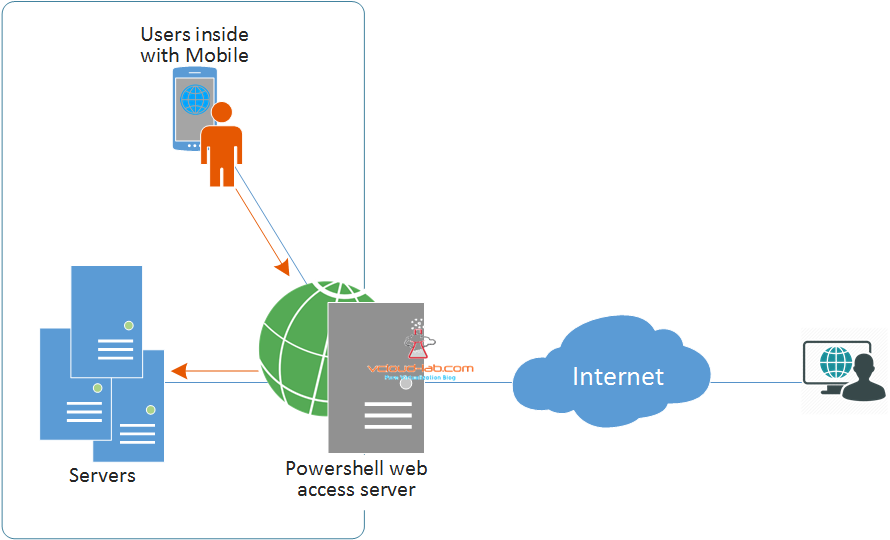
Microsoft PowerShell Web Access Server is a very cool method of accessing PowerShell over Internet from any supported browser. Microsoft had introduced this feature first in Windows server 2012 OS version. As in below diagram once Powershell web access feature service is installed on the server, and with few configuration server acts as proxy gateway, Users can access in-house servers over internet or from inside the organization. Mostly this feature is used by IT administrators. This is very handy for me, I have setup in my organization, when I am in meeting or cafeteria, and I get a call regarding issues, for minor issued I login to Microsoft PowerShell web console. and solve the problem in real time with my mobile.
GUI - SETUP AND CONFIGURE POWERSHELL WEB ACCESS SERVER (GATEWAY)
USE POWERSHELL ON MOBILE - SETUP AND CONFIGURE POWERSHELL WEB ACCESS (PSWA)
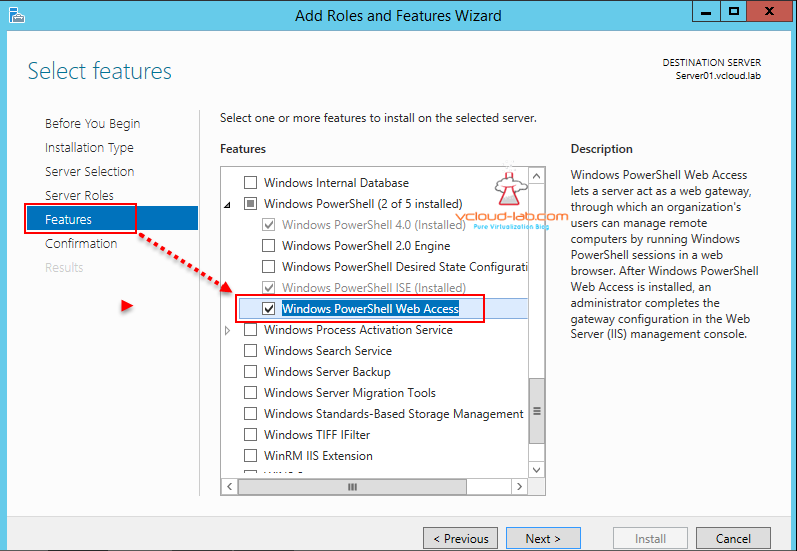
In this installation process I will setup and configure all the available GUI tools, I have created another Part of this article completely using powershell. I am using Server Manager GUI to install Powershell web access server feature. Open Server Manager and run Add Roles and Features Wizard, I have kept all the options defaults for Before You Begin, Installation type, server selection, server roles,, confirmation and results in wizard and mostly pressed Next.
I have only modified feature menu, and selected tick mark on Windows Powershell Web access sub service under Windows powershell feature. as shown in below screenshot. PSWA is dependent on IIS web server, It will be showing default IIS roles services it will be installing with this feature, Keep everything default and press install/finish in the last.
Microsoft description: Windows Powershell Web Access lets a server act as a web gateway through with an organization's users can manage remote comuters by running Windows PowerShell sessions in a web browser. After Windows PowerShell Web Access is installed, and administrator completes the gateway configuration in the Web Server (IIS) management console.
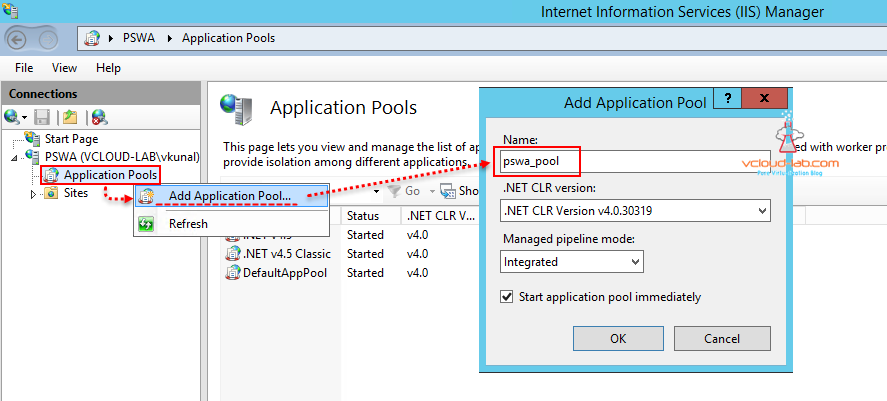
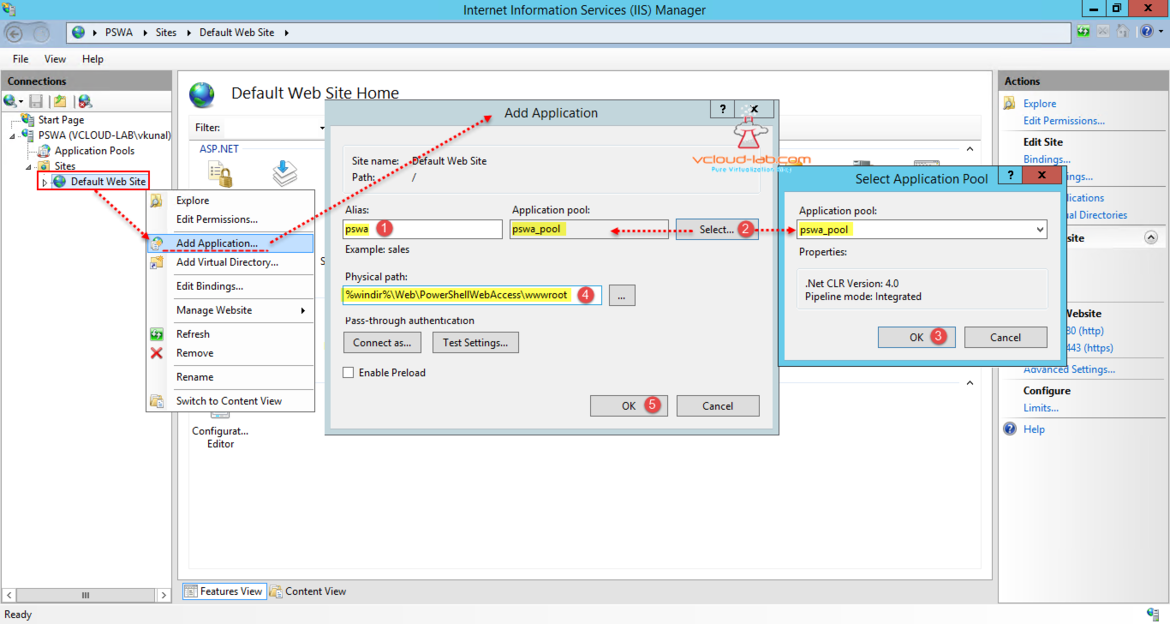
Once Windows PowerShell web access feature is installed successfully, Open IIS (Internet Information Services manger) from Control Panel\Administrative tools or server manager tools, Expand server name and right click add application pool. Give it Name pswa_pool, click ok.
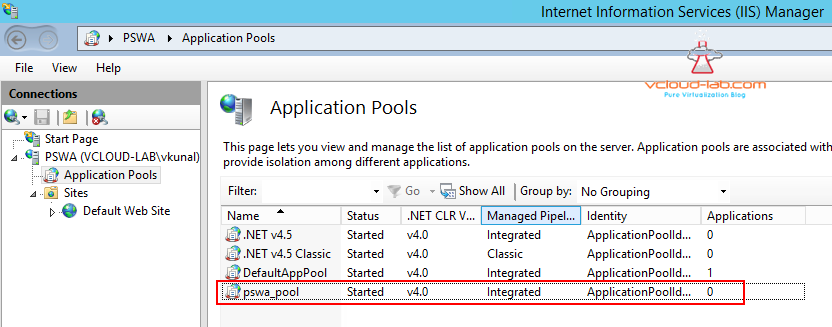
New application pool will be installed and it can be seen in the IIS manager under Application pools.
Next thing is crucial and I will add application. Give it alias name pswa. and select application pool earlier created from the drop down list. Physical path is important and it is %windir%\web\PowershellWebAccess\wwwroot by default. (%windir% is equal to folder c:\windows folder in most of the cases), This folder and contents are created once Powershell web access feature is installed.
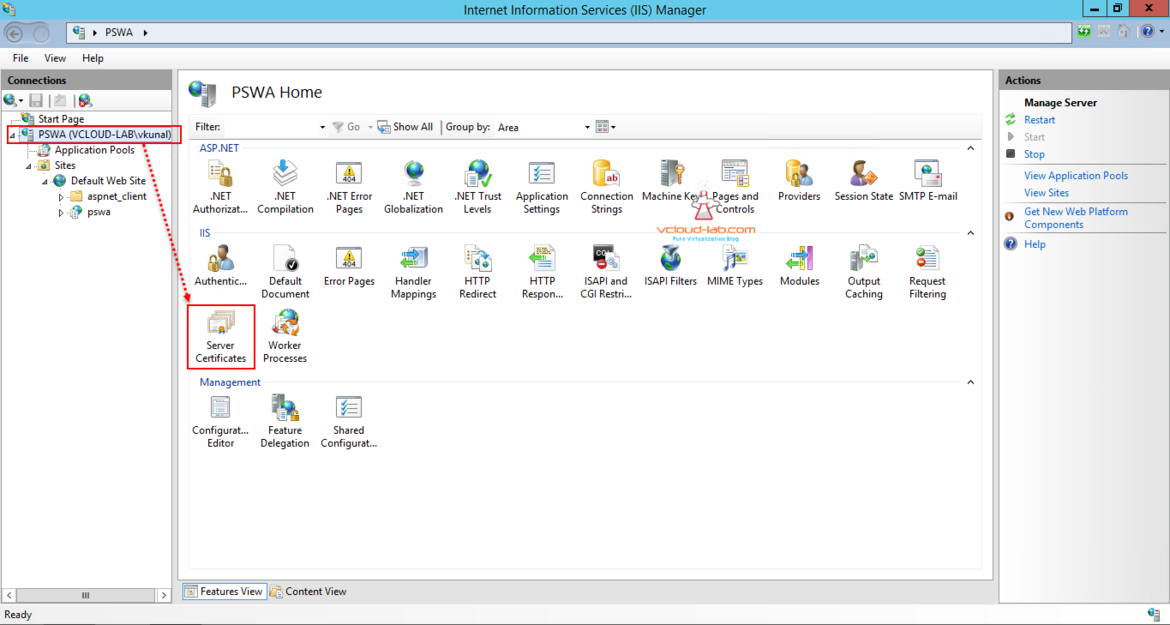
Once application is installed new application can been seen (pswa), As Powershell web access server doesn't work without ssl certificate, I will create one manually clicking on server name and SSL certificates.
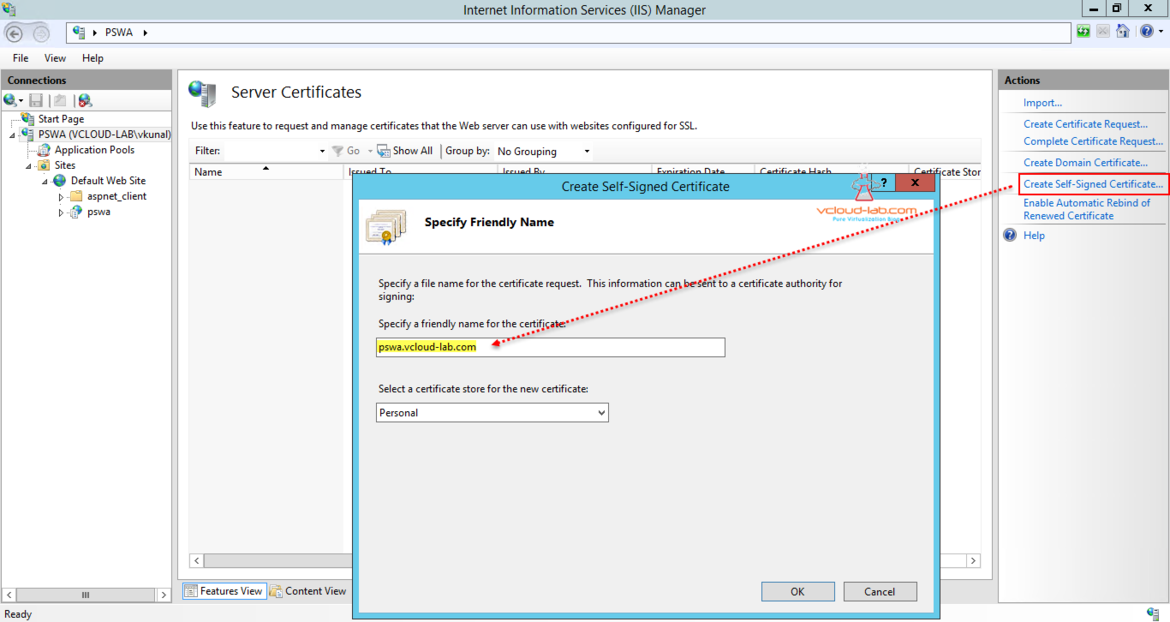
Currently I don't have any certificate, Click on self sign certificate, give it some friendly name, In my case I am keeping the same as hostname plus fqdn and it will be stored in personal certificate store. Later you can come here and add valid certificates.
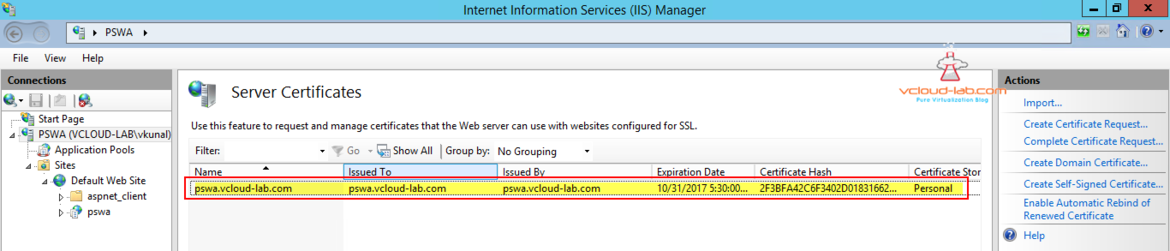
Once this self signed certificate is created I see all the related information in the list. Next step is to deploy certificate on Default web site, Note This certificate is valid for one year.
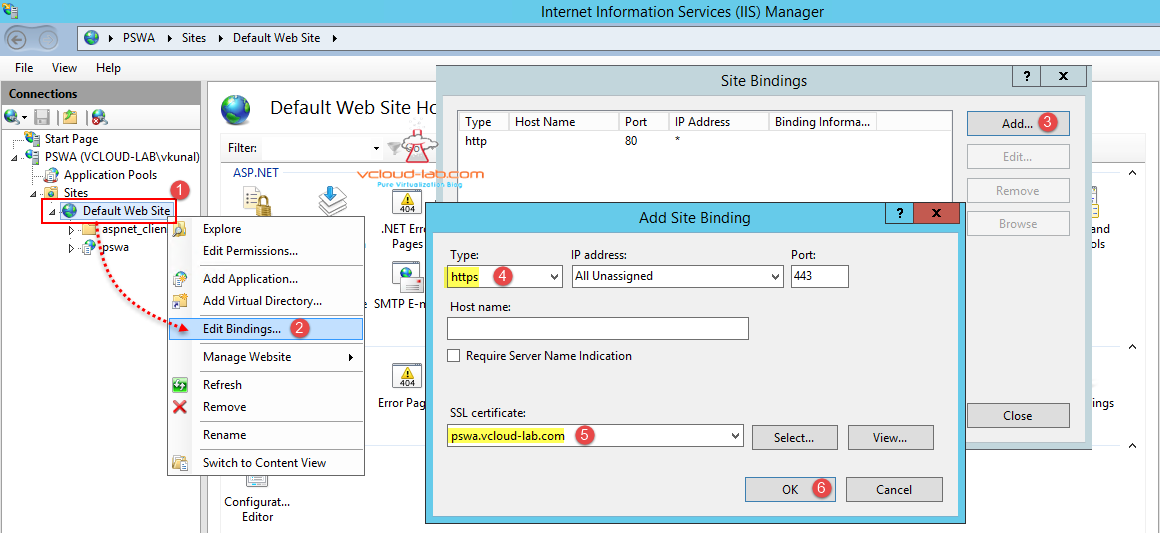
Right click on Default web site and click Edit Bindings to add and configure SSL website. In the drop down list of Type select https, and select the newly created self-signed SSL certificate, click ok.
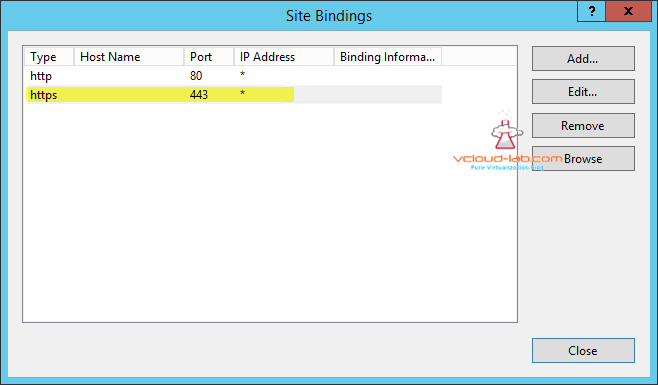
At this point IIS server is fully setup, Additional site binding for https port 443 looks like below, click close.
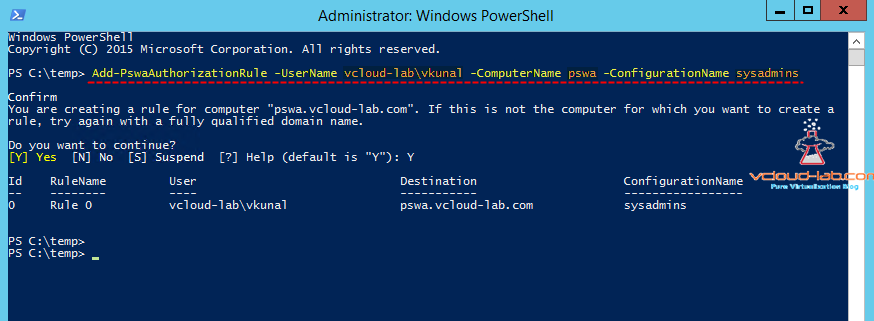
Next add powershell web access authorization rule (this is rule for access, Who (user) can access what (server)). Currently there is no compatible GUI for this process and need to perform this through only Powershell command. I have active directory user "vcloud-lab\kunal" and it can access only "pswa" server from Powershell console web browser.
Add-PswaAuthorizationRule -Username vcloud-lab\Kunal -ComputerName pswa -ConfigurationName sysadmins
New rule is added with Id 0 and Rulename will be Rule 0.
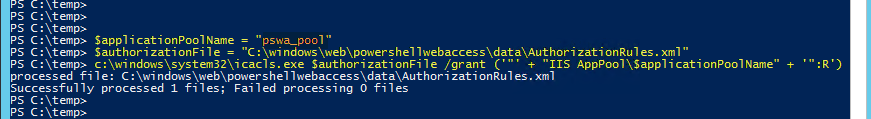
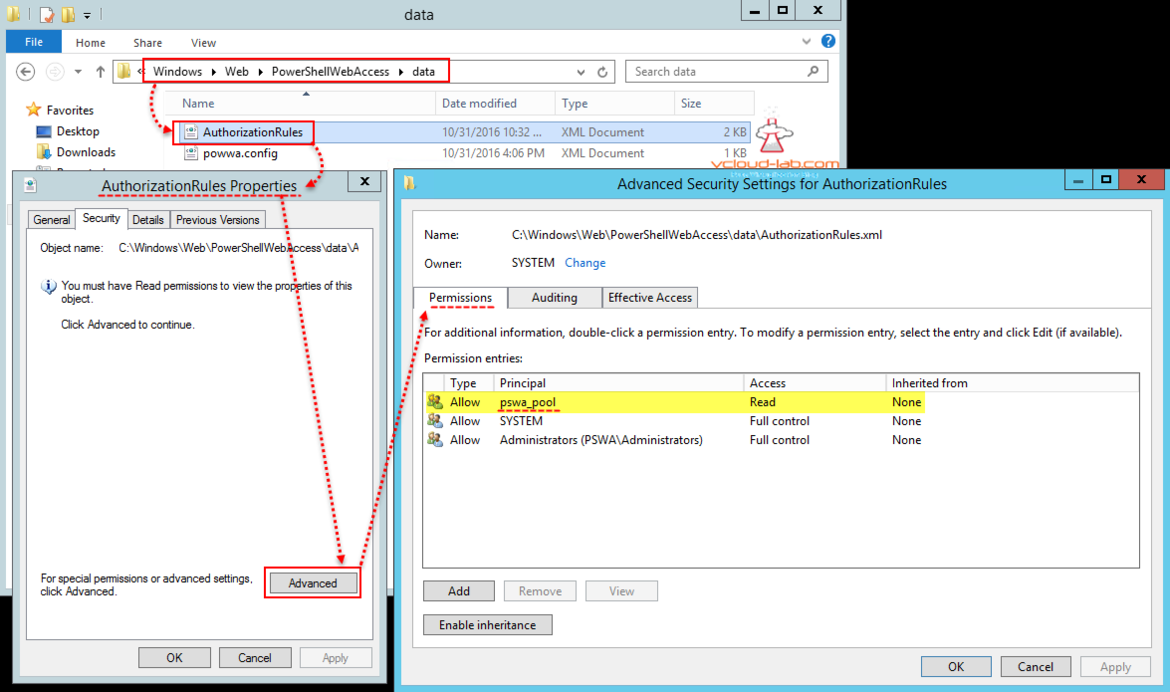
In next command assign read permissions to C:\windows\web\powershellwebaccess\data\AuthorizationRules.xml. This again can be done only through command line, "IIS AppPool\pswa_tool" will have read access to this file.
$applicationPoolName = "pswa_pool"
$authorizationFile = "C:\windows\web\powershellwebaccess\data\AuthorizationRules.xml"
c:\windows\system32\icacls.exe $authorizationFile /grant ('"' + "IIS AppPool\$applicationPoolName" + '":R') > $null
I can see on the AuthorizationRules.xml security properties, permissions for User "IIS AppPool\pswa_pool" is added with Read permissions.
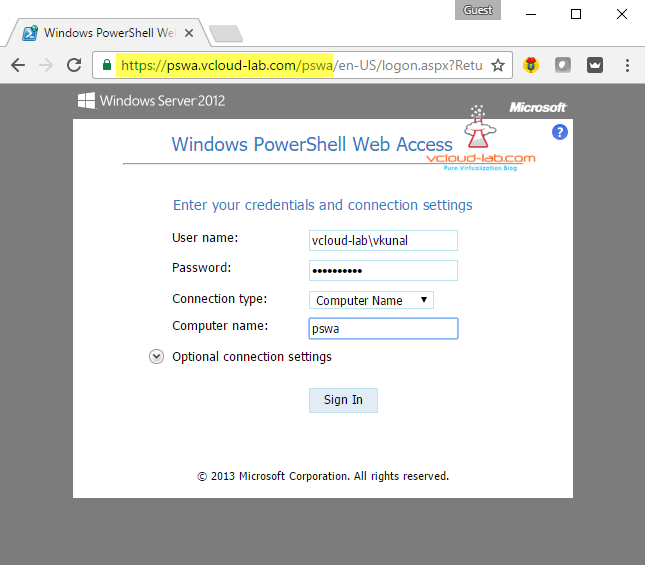
Complete configuration is done. Open any favorite browser and type url https://<ip or fqdn>/pswa. Type user name and password (in my case it is vcloud-lab\vkunal configured earlier in authorization rule and next is computer name pswa), this is what i added earlier in the rule, hit sign in.
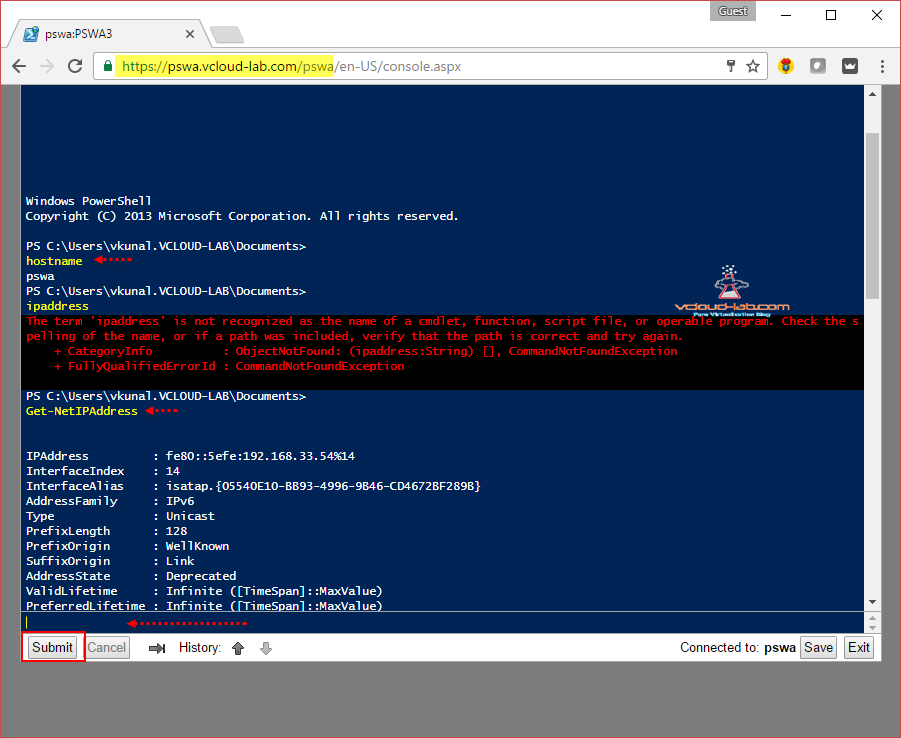
On the next page I can see the powershell console on the browser and commands can be executed.
Relevant posts on installing feature with all the screenshots.
PART 1 : INSTALL ACTIVE DIRECTORY DOMAIN CONTROLLER ON VMWARE WORKSTATION
USE POWERSHELL ON MOBILE - SETUP AND POWERSHELL WEB ACCESS (PSWA)