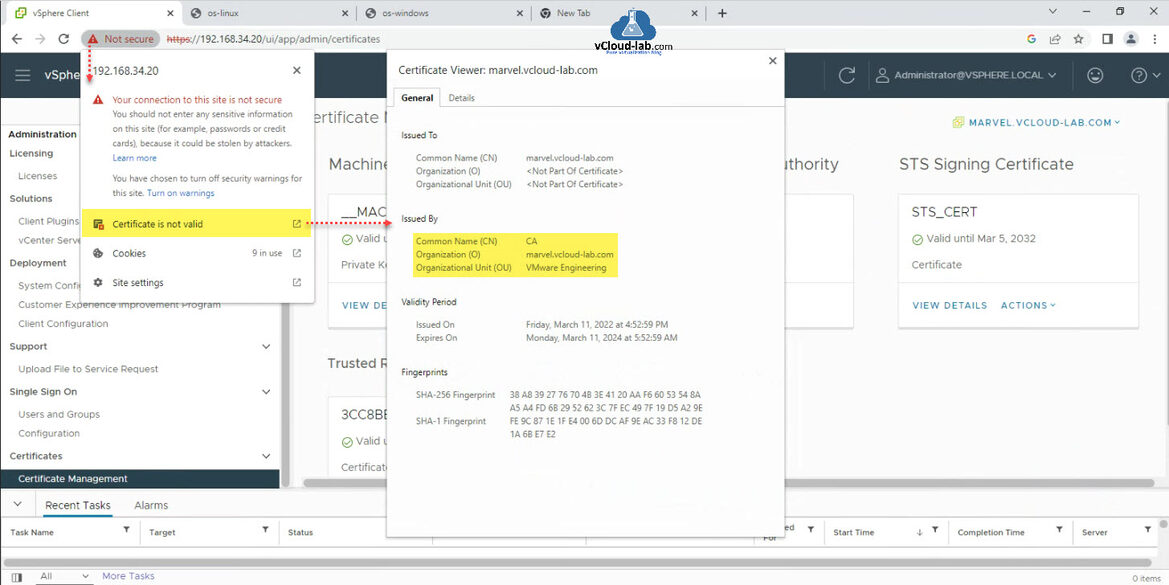
There is a best security practice to implement authorized SSL Certificates on VMware infrastructure. Here I am installing certificates on the vSphere vCenter server. By default VMCA (VMware Certificate Authority) signed certificate is installed on the vCenter server. Which you can see under vSphere Client >> Administration >> Machine SSL Certificate >> View details or you can check the same on the browser Not secure option it will show Certificate is not valid and you can see it is issued by VMware CA by clicking it.
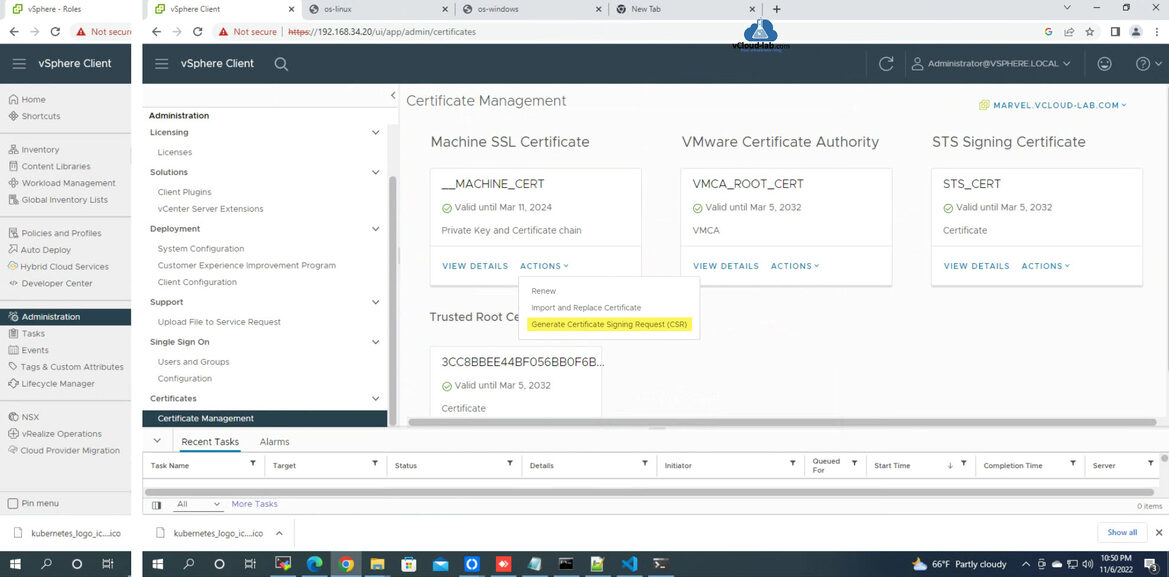
To replace the default VMCA assigned certificate Go to settings (3 bar button left top side) in vSphere Client, choose Administration from list. Navigate and expand to Certificates and go to Certificate Management. In the Machine SSL Certificate (__MACHINE_CERT box) click ACTIONS link and select Generate Certificate Signing Request (CSR).
It opens Generate CSR Wizard. Here enter information for a new SSL certificate. Info you need to provide is Common name (vCenter FQDN), Organization Unit, Country, State/Province, Locality, Email Address, Host (vCenter FQDN), Subject Alternative Name (Optional) (SANs), Private Key size. Click Next.
It will generate CSR as can be seen inside the box, Copy or download this CSR (Certificate signing request) as shown below, I will use and provide the content of this CSR in my Certificate Authority to be signed in the next task.
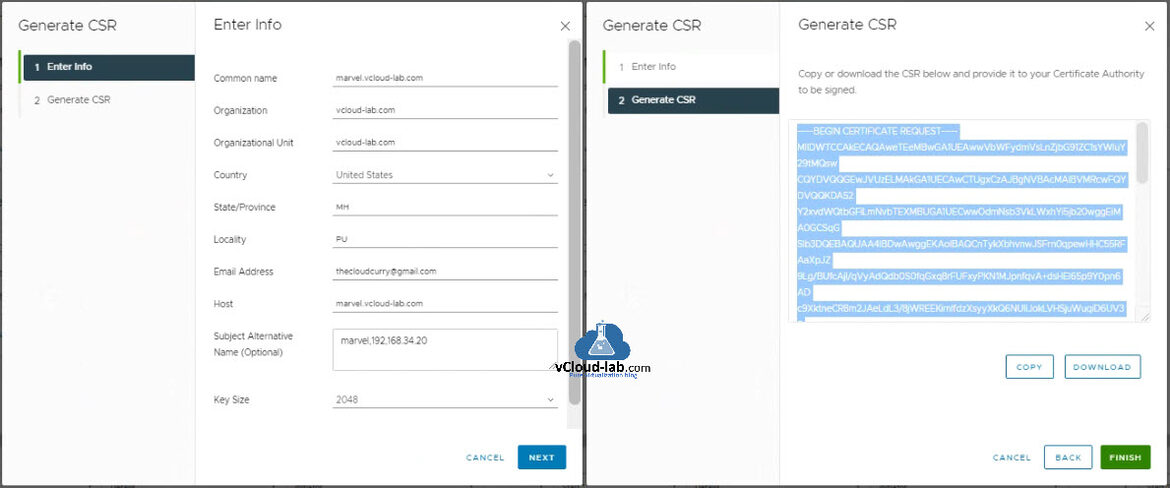
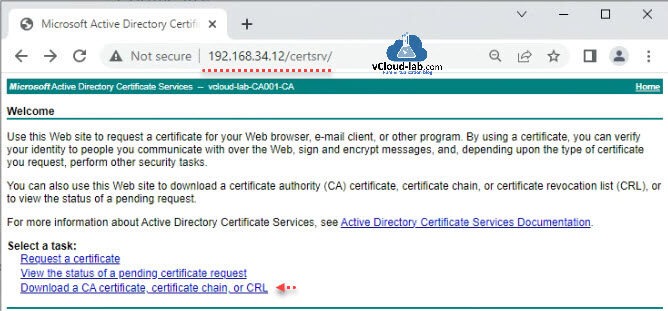
I am on my in-house Certificate Authority (Microsoft Active Directory Certificate Services) certsrv portal in the browser. Use this Web site to request a certificate for your Web browser, Email client, or other program. By using a certificate, you can verify your identity to people you communicate with over the Web, sign and encrypt messages, and depending upon the type of certificate you request, perform other security tasks.
Check this important article: Install and configure certificate authority (CA) on Microsoft Windows server with Group Policy
You can also use this Web site to download a certificate authority (CA) certificate, certificate chain, or certificate revocation list (CRL), or to view the status of a pending request.
Select a task by clicking Request a certificate. Submit an Advanced certificate request.
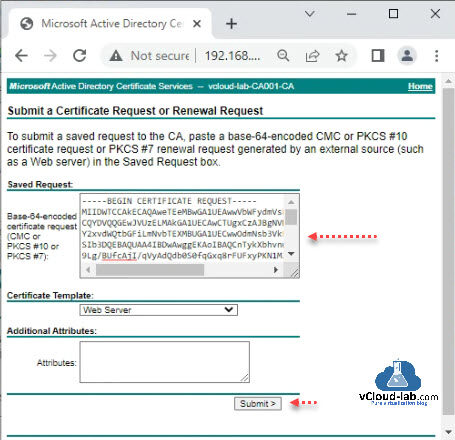
To submit a Certificate request or Renewal Request or saved request to CA, paste a base-64-encoded CMC or PKCS #10 certificate request or PKCS #7 renewal request generated by an external source (such as a Web server) in the Saved request box.
Here In the saved request the either use the CSR content copied or downloaded file from vCenter Server certificate management (Block from Begin to End). Change Certificate Template to Web Server.
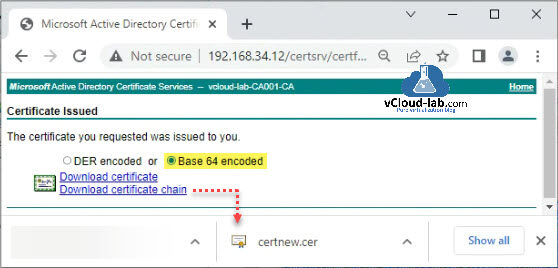
Select Base 64 encoded option and click Download Certificate for issued requested certificate.
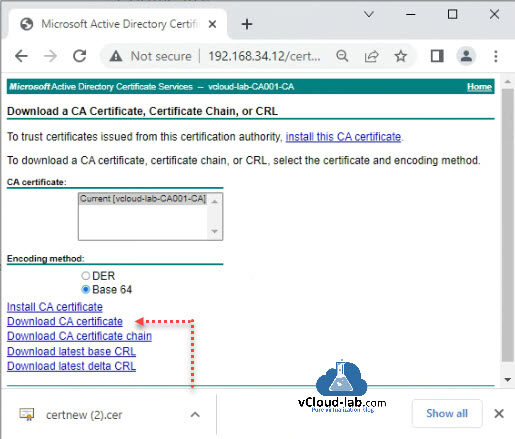
Next go back to the Welcome page of certsrv CA web portal. Click Download a CA certificate, certificate chain or CRL. This Root CA certificate will be required in the next step.
Click Download CA certificate and rename it to root.cer. I am keeping all certificate files in one directory. This Root CA certificate will be required in the next step.
Go back to vCenter Server >> Administrations >> Certificate management. Click on the Machine SSL Certificate >> ACTIONS button and choose Import and Replace Certificate.
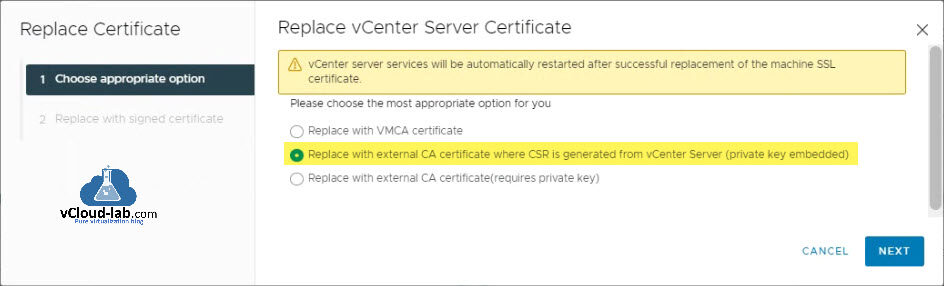
In the Replace vCenter Server Certificate Wizard, choose option Replace with external CA certificate where CSR is generated from vCenter Server (private key embedded) and click Next.
Note: vCenter Server services will be automatically restarted after successful replacement of the machine SSL certificate. So plan for proper vCenter server service's restart downtime.
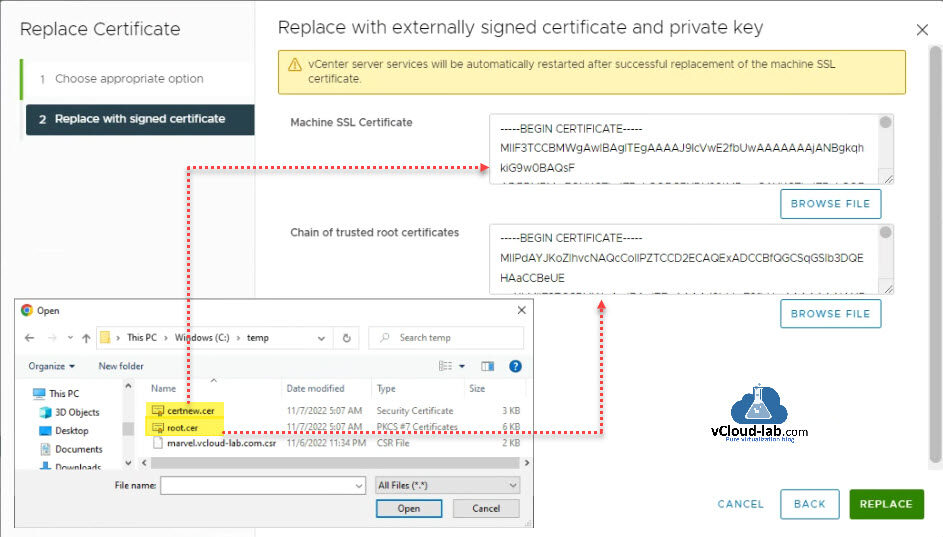
In the next page of Replace with externally signed certificate and private key under Machine SSL certificate BROWSE File and select certnew.cer file and in the Chain of trusted root certificates, select root.cer after clicking BROWSE File button. Click REPLACE button.
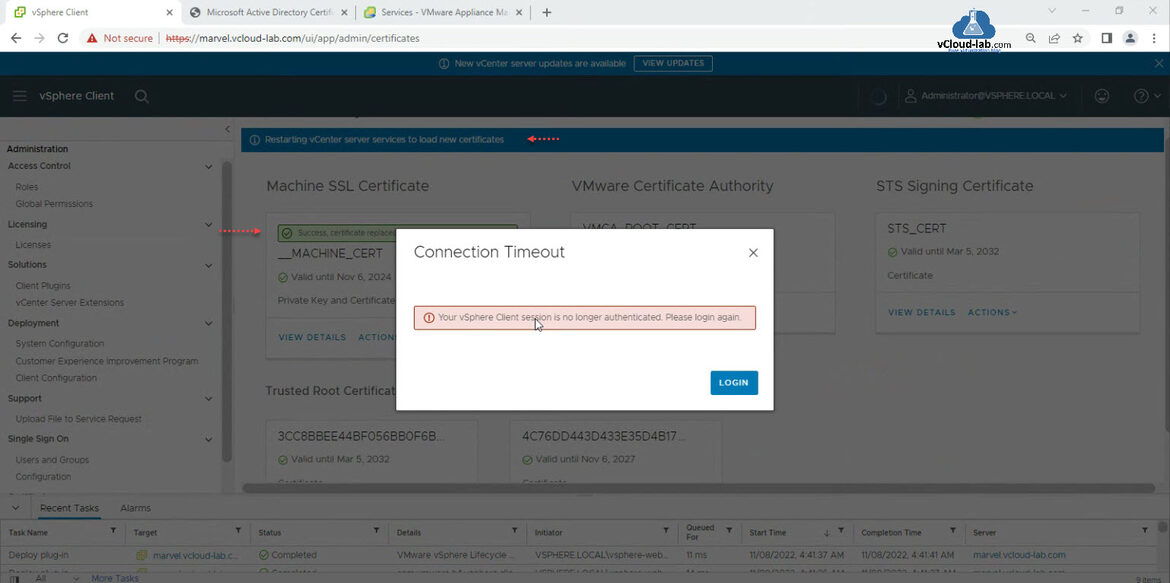
Once you click REPLACE button you will see behind there is a Success message as certificate replaced on vCenter server machine. Connection will Timed out and your vSphere Client session will no longer be authenticated. In the background vCenter Server services are being restarted, so it will take some time to come those services up and vCenter server get working.
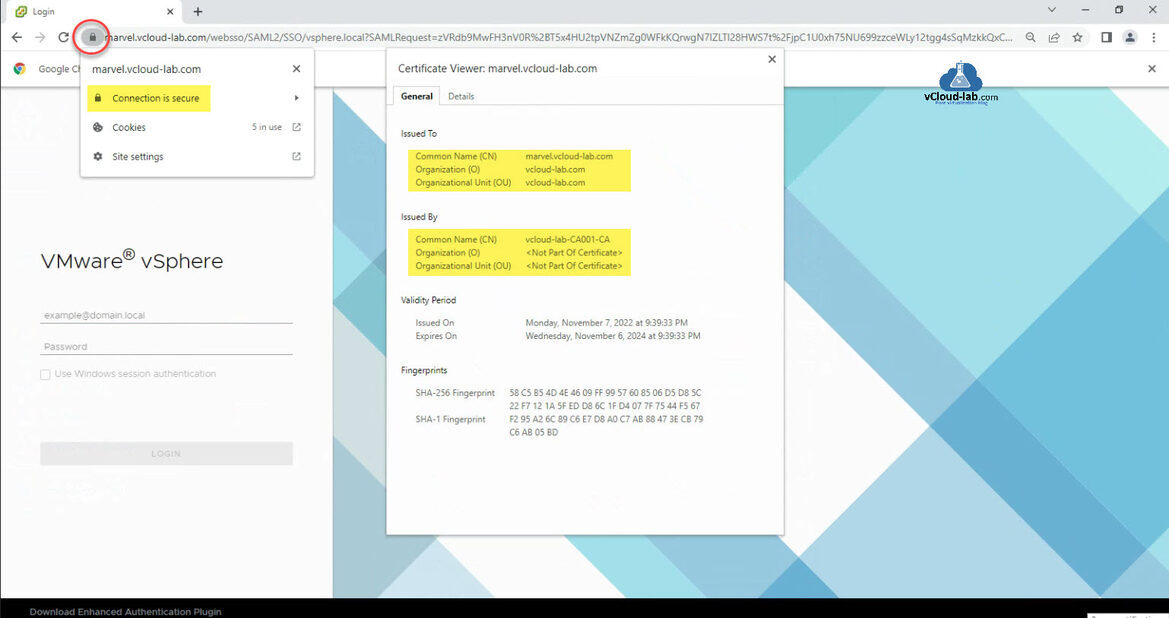
After few minutes refresh vCenter Server url in the browser, As you can see padlock sign with Connection is secure and the certificate issued successfully replaced by in-house Certificate Authority.
Useful Articles
VMware vCenter Esxi Add a Trusted Root Certificate to the Certificate Store
How to import default vCenter server appliance VMCA root certificate and refresh CA certificate on ESXi
How to replace default vCenter VMCA certificate with Microsoft CA signed certificate
Managing ESXi SSL certificate properties from vCenter server
Forward vCenter Server Appliance logs to syslog server
Connect-VIServer Error: Invalid server certificate. Use Set-PowerCLIConfiguration
VMware vcenter 7.0 A problem occurred during setup Services might not be working as expected 63%
VMware UMDS curl_easy_perform() failed: cURL Error: SSL peer certificate or SSH remote key was not OK, SSL certificate problem: unable to get local issuer certificate