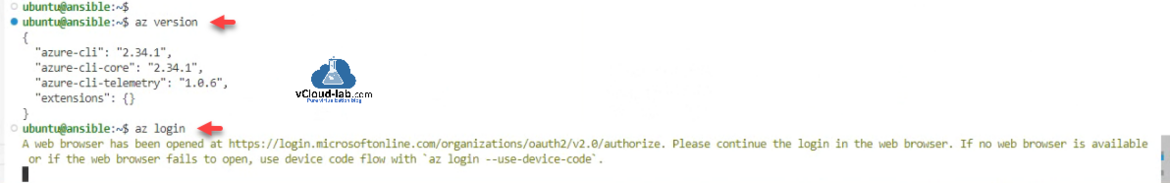
This article is first part of Deploy create Virtual Network vNET in Azure cloud using Ansible Here I am going to show multiple ways to authenticate Ansible with Microsoft Azure cloud. Very first method is very simple using azure az cli. Make sure you have installed azure cli application on linux where ansible playbooks will be executed. Use below command to login and try your Ansible yaml playbook scripts.
az login
Azure AZ CLI works great in all cases.
 Another method is using Azure App registrations, this works great when you are doing automation and don't have to worry about multi-factor authentication plus minimal required access control. You can check Create an Azure App registrations in Azure Active Directory using PowerShell & AzureCLI.
Another method is using Azure App registrations, this works great when you are doing automation and don't have to worry about multi-factor authentication plus minimal required access control. You can check Create an Azure App registrations in Azure Active Directory using PowerShell & AzureCLI.
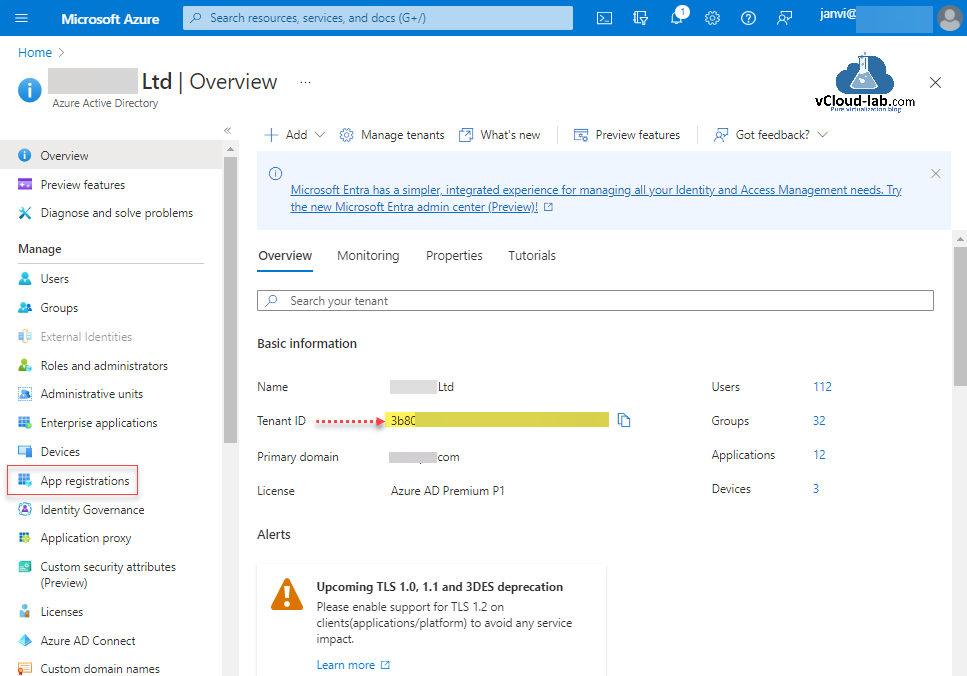
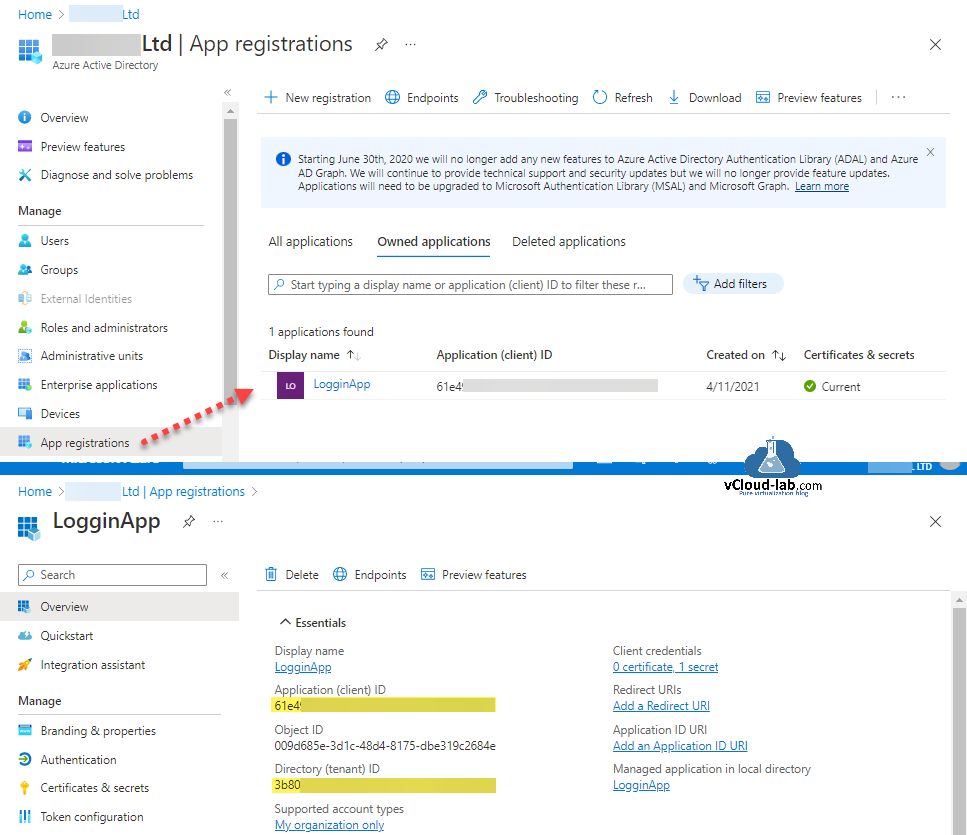
When using app registration aka service principals you need 4 object ids/values First is Tenant ID, which You can find on Azure Active Directory portal >> Overview >> Tenant ID. Second is Subscription ID, which you can find searching for Subscription on Azure Portal.
Check this article: Ansible authenticate to Microsoft Azure using credential profiles Part 2
In the last App Registrations (Service Principal) in located under Azure Active Directory, check Under Owned Applications tab. Once you click the service principal grab the IDs for Application (client) ID and Directory (tenant) ID. Make sure you have assigned correct RBAC roles and permissions to app registrations in azure subscription to create resources.
Check on: Create an Azure App registrations in Azure Active Directory using PowerShell & AzureCLI
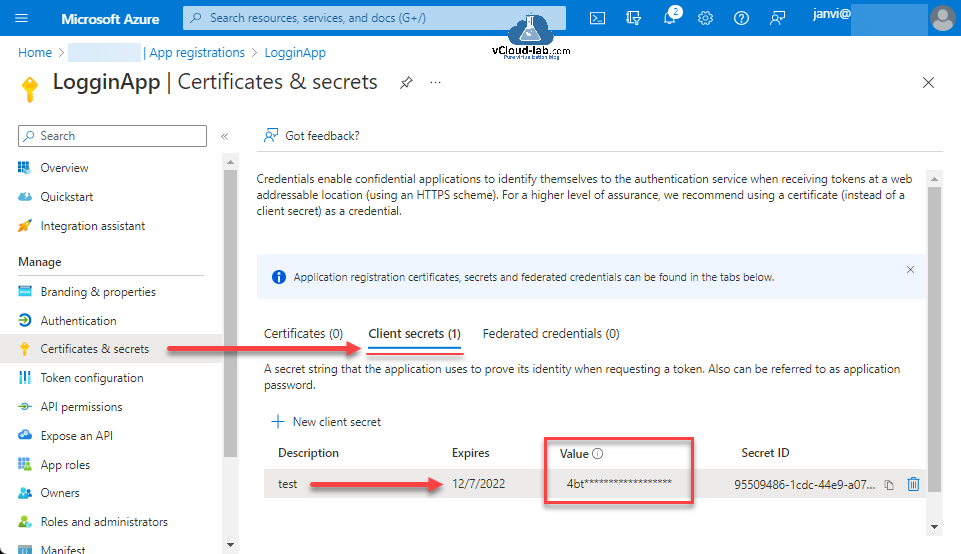
For secret click Certificates & secrets, Under Client secrets generate one new client secret. C.lient secret values cannot be viewed, except for immediately after creation. Be sure to save the secret when created before leaving the page.
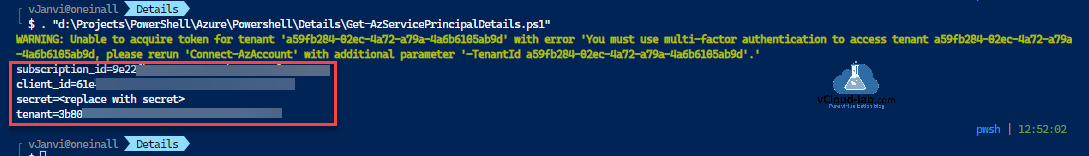
To make it easier I have written below PowerShell script to grab the details subscription_id, client_id and tenant. Secret value can only be viewed at the time of creation after it is masked forever. So note down your secret value and keep it safe.
Check this out: Ansible authenticate to Microsoft Azure using credential inside yaml file
$subscriptionName = 'Sponsership-by-Microsoft' $appRegistrationName = 'LogginApp' $subscription = Get-AzSubscription -SubscriptionName $subscriptionName $servicePrincipal = Get-AzADApplication -DisplayName $appRegistrationName @" [default] subscription_id=$($subscription.Id) client_id=$($servicePrincipal.ApplicationId.Guid) secret=<replace with secret> tenant=$($subscription.TenantId) "@
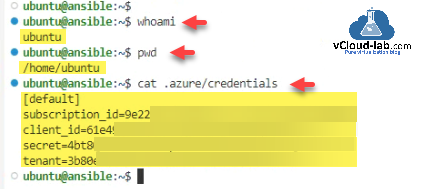
Now use the information on linux where Ansible is installed. Create a folder and file inside home users directory as a path ~/.azure/credentials. and save the content something like below with gathered azure credentials info and run yaml ansible playbook to test authentication to Microsoft azure.
For test ansible playbook use: Deploy create Virtual Network vNET in Azure cloud using Ansible
[default] subscription_id=xxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx client_id=xxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx secret=xxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx tenant=xxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx
Useful Articles
Create a Azure Virtual Network with Subnet using PowerShell
Azure automation account DSC for On-Premise Virtual Machine on boarding
Azure Powershell : Operation returned an invalid status code 'BadRequest'
Create an Azure Automation account on using Portal PowerShell and AzureCLI
Gather Azure Virtual Network inventory information using PowerShell
Get Azure virtual machine backup reports using Powershell
Why is my Azure recovery services vault not getting deleted?
Microsoft Azure PowerShell cmdlet 'this.Client.SubscriptionId' cannot be null
Azure PowerShell Get-AzStorageShare Could not get the storage context